- European DIY marketplace ManoMano disclosed a third-party breach affecting about 38 million individuals after attackers compromised a customer support provider linked to the company. Reported exposed data included names, email addresses, phone numbers, and customer service interactions, while ManoMano said passwords were not compromised and internal systems were not breached.
- The breach showed how a connected support environment can become a path to customer data at scale when it can access a centralized dataset.
Why Third-Party Data Exposure Is a Growing Risk for Online Marketplaces
Online marketplaces depend on support providers, CRM platforms, logistics tools, payment services, and analytics vendors. Those integrations improve speed and scale, but they also expand the number of systems that can reach customer data.
In ManoMano’s case, public reporting links the breach to a compromised third-party customer support provider and a Zendesk environment connected to the company.
For CISOs and regulated enterprises, the issue is concentration. When a connected environment can search, export, or retain customer records at scale, that environment becomes part of the enterprise attack surface and a practical route to bulk exfiltration.
What Happened
ManoMano said it identified unauthorized access in January 2026 and later determined that about 38 million individuals were affected. The exposed data reportedly included names, email addresses, phone numbers, and customer service communications. The company said it revoked the subcontractor’s access, strengthened access controls and monitoring, notified French authorities, and warned customers to watch for phishing and social-engineering attempts. (BleepingComputer)
Attackers compromised a third-party customer support provider and reached a support environment tied to ManoMano rather than the company’s internal production systems. SecurityWeek reported that the data was allegedly taken from a Zendesk instance and may have included information tied to 37.8 million accounts.
Technical Cause
The full forensic details are not public, but the failure pattern is clear from the reporting. (SecurityWeek)
| Component | Failure |
| Third-party support provider | Compromised external service handling customer interactions |
| Support platform access | Broad visibility into customer records and support histories |
| Data architecture | Large dataset reachable from one connected environment |
| Security boundary | Vendor compromise created a direct path to sensitive data |
The core issue was concentration. A connected support environment appears to have had access to enough centralized customer data to make bulk extraction valuable. That is what allowed the breach to scale. (TechRadar)
Governance and Risk Implications
This breach shows why vendor risk becomes architectural risk when suppliers can reach concentrated datasets. Many organizations maintain a supplier inventory, but fewer maintain a live map of which external systems can search, export, or store sensitive data in bulk.
That gap matters. If support platforms, subcontractors, or adjacent tools hold replicated customer records, the enterprise may be operating multiple breach targets. Contract clauses and vendor assessments still matter, but they do not stop mass extraction if a connected system can still reach a large dataset.
At this scale, the exposure creates notification burdens, raises phishing risk against customers, and invites regulatory scrutiny across the supply chain. ManoMano’s reported notifications to CNIL and ANSSI underline that point. (TechRadar)
How to Prevent Third-Party Data Breaches in Online Marketplaces
Third-party platforms often need access to customer data to support billing, CRM, service delivery, and operational workflows. The priority is to limit how much data a connected environment can store, view, export, or retain at scale.
Where possible, avoid bulk replication into vendor systems. External providers should access only the data required for the task, under tightly scoped permissions, restricted export controls, and defined retention limits. That reduces the amount a compromised environment can expose, even when third-party platforms remain operationally necessary.
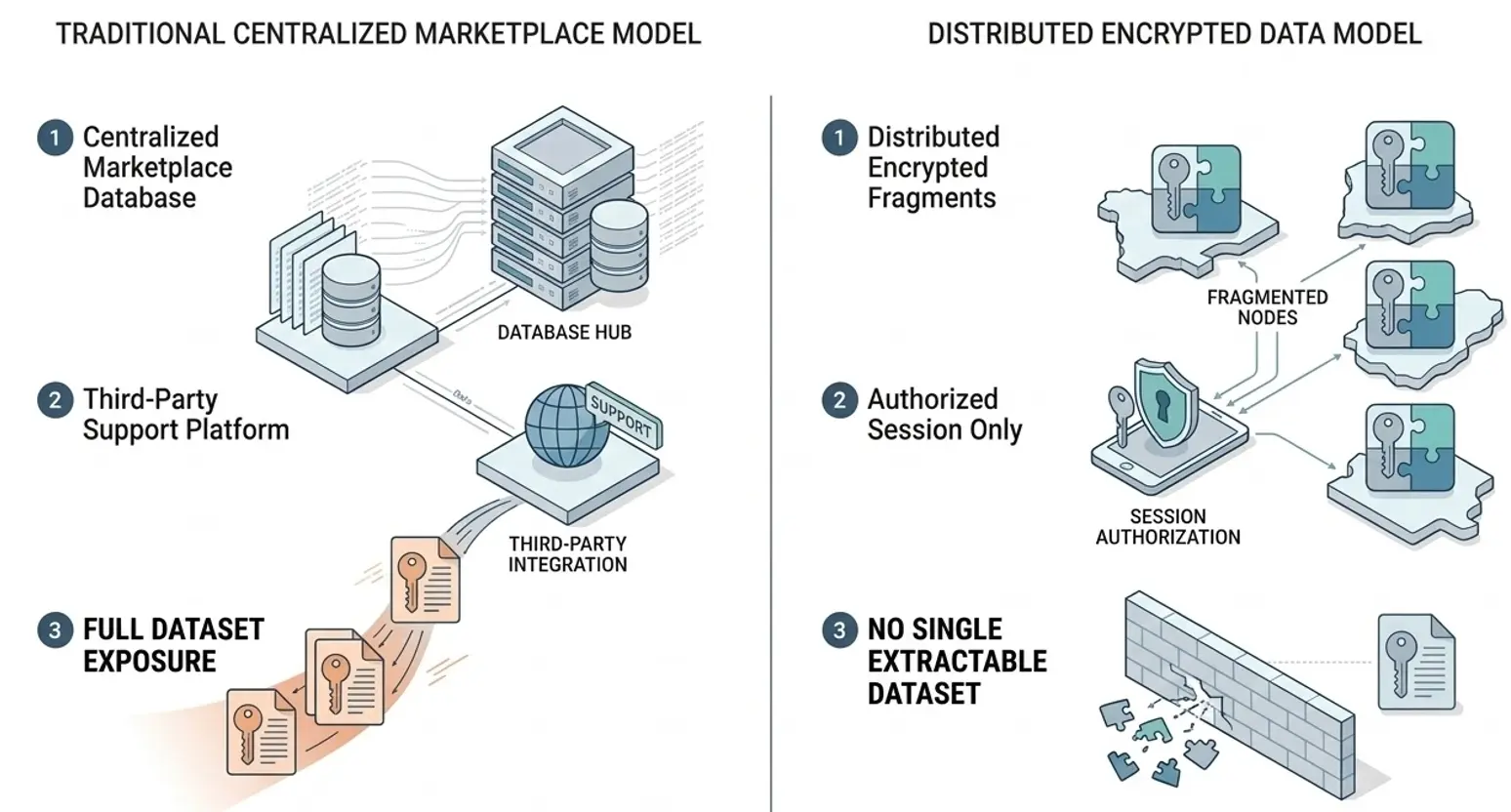
To defend against a third-party compromise that grants wide access to customer records or critical data, adopt an architecture where no complete dataset ever resides in, or is accessible from, any single connected system or vendor environment.
Entropya’s Digital Dead Drop (D3) uses a distributed synchronization model with the ML-KEM post-quantum cryptography (PQC) to fragment and disperse sensitive data across a global network of transit nodes. Fragments move via randomized IP addresses and untraceable transport pathways. Reassembly requires explicit session-bound authorization.
Even if a third-party support platform is breached, attackers obtain only isolated encrypted fragments which reduces bulk data exposure and extraction.
Review Your Third-Party Data Architecture
See how Entropya’s D3 architecture helps reduce bulk data exposure by removing the single extractable dataset attackers target in third-party breaches.